
Feb 24, 2026
In this article, you will discover why more and more companies are being hit by cyber attacks, and how to avoid being next. We will identify the biggest risks and share 7 ready-to-implement tips to keep your organization cyber-secure now and in the future.
Written by Jill, Content Manager - Written: May 19, 2025 - Last updated: March 16, 2026
Cyber attacks are a growing threat to businesses of all sizes: the FBI’s Internet Crime Complaint Center logged 859,532 complaints in 2024 with losses topping $16 billion, while the UK’s Cyber Security Breaches Survey 2025 found 43 percent of businesses suffered a breach or attack. This article explains how cyber criminals operate, what risks your organization faces, and provides 7 practical tips to protect your company.
The good news is that companies do not stand alone. Public programmes such as CISA’s Shields Up in the US and the NCSC’s Cyber Essentials in the UK offer guidance, while digital tools provide protection. Whether you run a small firm or a multinational, addressing cyber security is no longer an option, but a necessity.
| Statistic | Source |
|---|---|
| 1,925 weekly cyber attacks per organization in Q1 2025 (up 47%) | Check Point Research |
| Education most attacked sector: 4,484 weekly attacks | Check Point Research |
| $16 billion in FBI-reported cybercrime losses in 2024 (up 33%) | FBI |
| $10.5 trillion estimated global cybercrime cost per year by 2025 | Statista |
| $4.88 million average cost of one data breach in 2024 (up 10%) | IBM |
| Cyber insurance premiums expected to double from $14B to $29B by 2027 | Munich RE |

Cyber security is everything your company does to protect itself from digital threats. Think of it as locking the door when you leave: you turn on the alarm, close the windows and doors, and don’t leave anything of value unattended. The digital world works the same way, but instead of locks and alarms, you use passwords, firewalls, and encrypted data.
In practice, cyber security means:
Never before have businesses been so digitally connected, yet so vulnerable. Hackers are becoming more professional and their methods more sophisticated. The consequences of a cyber attack can be severe:
Legislation around digital security is also on the rise. Governments are imposing increasingly stringent requirements on how companies handle data. Think of the GDPR, which dictates how you must protect and report personal data in the event of a data breach, and new European directives such as the NIS2 Directive, which imposes additional obligations on many sectors from 2024. Failure to comply with these regulations can result in hefty fines and a big dent in your image.

Cybercriminals are using increasingly sophisticated techniques to infiltrate organizations. Unfortunately, it doesn’t have to be complicated: an inattentive employee or a small human error can be all it takes.
These are spoofed emails or websites that appear to be from a well-known organization, such as a bank, a colleague, or a supplier. Employees are tricked into clicking a link, logging in, or opening an attachment. With a simple click, hackers can gain instant access to confidential company information or login credentials.
In a ransomware attack, cybercriminals use malicious software to gain access to your systems. They then hold your computer systems or important files hostage. Only after a ransom is paid will you (perhaps) regain access to your own data. Ransomware can bring entire businesses to a standstill, often resulting in significant financial loss.
Are you using unsecured Wi-Fi or is your corporate network open to everyone? If so, you are giving cybercriminals free rein. They can easily penetrate systems to steal data or install malware, often without you noticing.
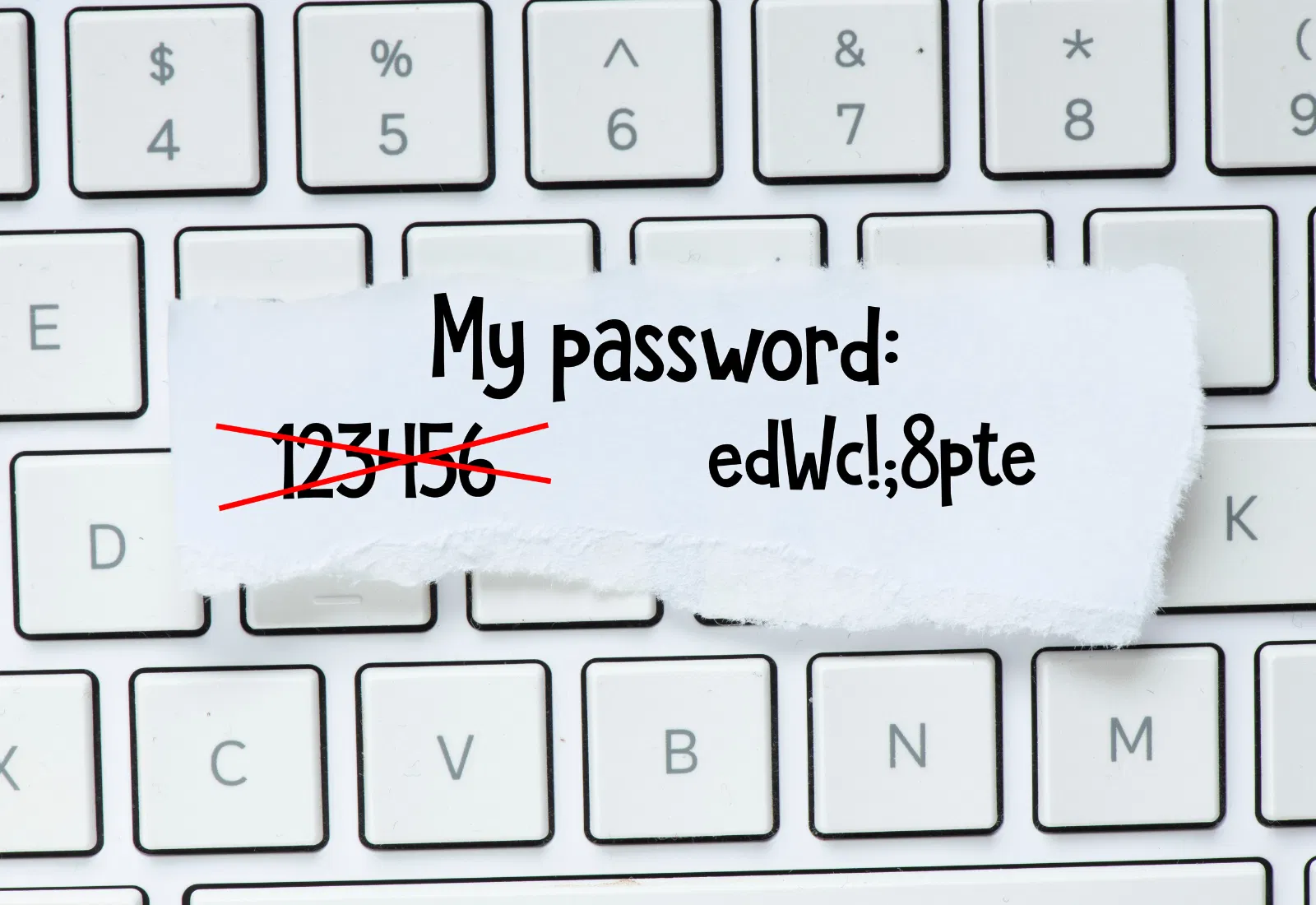
An easy-to-guess password, such as “Welcome123” or “Company2025,” is child’s play for hackers. Password reuse is also dangerous: if data leaks out through another party, hackers can easily try to see if the same password works with your company.
Some cybercriminals use programs (bots) that continuously scour the Internet for vulnerabilities in outdated software or poorly secured systems. If such a bot finds a vulnerability, it immediately tries to exploit it to gain access to your network or install malware. Often companies don’t notice this until it’s too late.
In a DDoS attack (“Distributed Denial of Service”), attackers send enormous amounts of traffic to your website, web shop or platform via thousands of hacked computers at the same time. As a result, it becomes overloaded and inaccessible to customers. With such an attack, criminals try to disrupt your business operations, sometimes to extort a ransom or purely for sabotage.
A password manager stores your passwords in encrypted form, automatically generates strong, unique passwords, and fills them in as needed. Combined with multi-factor authentication (an extra verification question or code on your smartphone), you’ll make things really difficult for hackers.
In May 2017, the world was hit with the infamous WannaCry ransomware. This attack exploited a vulnerability in Microsoft Windows, for which an update had been released months earlier. Unfortunately, many organizations had not yet installed the update. This allowed the hackers to quickly infect hundreds of thousands of computers in more than 150 countries.
People are the weakest link when it comes to cyber security. Invest in awareness: teach your employees how to recognize suspicious emails and phishing attempts, and discuss how to handle company data safely.
Not everyone needs access to all files or systems. An intern does not need access to financial reports, and a receptionist does not need access to the entire CRM system. Make sure that only authorized employees have access to sensitive data. Adjust permissions when someone changes positions or leaves the organization, and periodically check who has access to what.
Establish a clear backup strategy. Automatically back up important company data and systems - ideally daily or weekly - and also store backups offline or in a secure remote location. Regularly test whether you can actually restore files.
With digital visitor registration, you avoid having paper visitor lists lying around that may contain sensitive information. Modern systems store visitor data securely and in encrypted form, so unwanted people cannot access it, and you are instantly compliant with data protection laws.
Want to learn more about how digital visitor registration can make your business more secure? You can read all about it in this article. Integrating your visitor management system with an access control system ensures optimal security for your organization.
Know what to do if things do go wrong. Have a clear roadmap when you suspect a cyber incident: who should you contact first, which systems should be shut down, and who informs customers and partners? Establish responsible parties and practice this plan regularly by organizing a “cyber fire drill,” for example.
Cyber security is not a one-time action, but a process. By applying these tips structurally, you will help your organization stay safe and resilient in the digital age.
Count the number of times you can answer “yes”. The more check marks, the more cyber-secure your company is. Are there still areas of concern? Start working on those today, because every step counts.
Cybercriminals are getting smarter, and businesses are more vulnerable than ever. Even a small mistake or a forgotten update can have major consequences. Fortunately, cyber security does not have to be a complicated or time-consuming process. Even something as simple as digitizing your visitor registration can make a big difference in your company’s security and protection of sensitive information.
Don’t wait until something goes wrong. Take the first step toward a cyber-secure business today. Start simple: pick an item from the checklist, address it with your team, and work on it one step at a time. You’ll build trust with your customers and partners… and sleep better at night.
Wondering how digital visitor management can help you run a secure and professional business? Start a free trial and see the difference. Do you have any questions or would you like tailored advice? Chat with us or book a demo. Together we will make your reception area and your business more cyber-secure.